What is DORA Europe and How Does It Impact Financial Institutions?
- Feb 17
- 10 min read
The Digital Operational Resilience Act (DORA Europe) is a binding European Union regulation that mandates how financial institutions and their critical ICT providers manage digital risk. It requires these organizations to prove they can withstand, respond to, and recover from all types of ICT-related disruptions and threats, effectively making proactive digital resilience a legal obligation.
What Is the Core Purpose of the DORA Europe Regulation?
The core purpose of DORA Europe is to harmonize and strengthen the digital operational resilience of the EU's financial sector. It aims to ensure that all financial firms can maintain critical operations during a severe digital disruption, preventing a cyber incident at one entity from causing a domino effect across the interconnected market.
DORA consolidates various ICT risk management rules into a single, comprehensive framework. For Chief Information Officers (CIOs) and IT leaders, this shifts the focus from merely preventing cyberattacks to demonstrating and continuously testing the ability to operate through them. The regulation moves the industry from suggested best practices to legally enforceable standards.
Which Organizations Must Comply with DORA?
DORA applies to a broad spectrum of over 20 types of financial entities and their critical ICT third-party service providers. This wide scope acknowledges that modern finance is an interconnected ecosystem where a disruption in the digital supply chain can have systemic consequences, affecting thousands of organizations.
The regulation's scope includes:
Traditional Financial Institutions: Banks, credit institutions, and investment firms.
Insurance and Reinsurance Undertakings: Companies managing significant risk and capital.
Payment and E-Money Institutions: Entities at the heart of digital transactions.
Crypto-Asset Service Providers: Recognizing the growing role of digital currencies.
Critical ICT Third-Party Providers: This includes major cloud service providers, software vendors, and data analytics firms whose services are integral to financial operations.
The Digital Operational Resilience Act officially entered into force on January 16, 2023, with a final compliance deadline of January 17, 2025. Research shows that a staggering 94% of financial institutions are actively working to understand and implement DORA's requirements, impacting an estimated 22,000 organizations across the EU.
What Are DORA's Five Key Pillars?
DORA's framework is built upon five interconnected pillars that collectively create a holistic approach to managing digital risk. Each pillar addresses a specific area of resilience, ensuring organizations have a complete strategy covering everything from internal controls to supply chain vulnerabilities. You can explore these pillars in more detail in our comprehensive guide on DORA regulation.
Pillar | Primary Objective |
|---|---|
ICT Risk Management | Establish a robust and comprehensive framework to identify, protect against, detect, respond to, and recover from ICT-related risks. |
ICT-Related Incident Reporting | Create a standardized process for classifying and reporting major ICT incidents to regulatory authorities, eliminating ambiguity. |
Digital Operational Resilience Testing | Implement a proportional, risk-based program of advanced security testing, including mandatory Threat-Led Penetration Testing (TLPT) for critical firms. |
ICT Third-Party Risk Management | Proactively manage the risks associated with relying on third-party technology providers through specific, mandatory contractual requirements. |
Information and Intelligence Sharing | Encourage financial entities to share cyber threat information and intelligence with one another to strengthen the collective defense of the sector. |
How Does DORA Impact Your ITSM and ITOM Processes?
The DORA Europe regulation directly mandates strengthening your core IT Service Management (ITSM) and IT Operations Management (ITOM) processes. DORA’s rules are not abstract legal concepts; they are practical requirements that integrate directly into the daily workflows managed by platforms like ServiceNow, HaloITSM, and Freshservice.
Your service management platform becomes the operational engine for DORA compliance. The regulation’s focus on robust ICT risk management is built upon the foundation of mature Incident, Problem, and Change Management disciplines. DORA effectively transforms these operational best practices into legally required and auditable controls, allowing you to leverage your existing investments in service management tools and teams.
How do DORA's requirements map to ITSM/ITOM?
DORA’s pillars align directly with standard processes and modules within leading service management platforms. This mapping provides a clear roadmap for connecting the regulation's demands to your existing operational capabilities, transforming your ITSM tool into a powerful compliance engine without needing a whole new suite of software.
DORA Requirement Pillar | Relevant ITSM/ITOM Process | Key Platform Capabilities (ServiceNow, HaloITSM, etc.) |
|---|---|---|
ICT Risk Management | Incident Management, Problem Management, Change Enablement | Automated incident categorization, root cause analysis (RCA) tracking, risk assessment workflows for changes. |
ICT-Related Incident Reporting | Incident Management | SLA timers, automated notifications, reporting dashboards configured to regulatory timelines and formats. |
Digital Operational Resilience Testing | CMDB, Service Mapping, Disaster Recovery Planning | Dependency mapping, business impact analysis (BIA), orchestration of DR test plans and result tracking. |
ICT Third-Party Risk | Vendor Management, Contract Management | Centralized vendor risk profiles, performance monitoring (SLAs), and contract lifecycle management. |
How does DORA reshape incident management?
DORA elevates incident management from a service restoration function to a structured, rapid, and reportable compliance activity. The regulation imposes strict timelines for incident classification, response, and reporting that many organizations are not currently equipped to meet, requiring a shift in both process and platform configuration.
Your ITSM platform must be configured to automatically classify incidents based on DORA's severity criteria. Standard operating procedures for major incidents need to be documented and embedded directly into your workflows. The goal is to prove you have a controlled, repeatable process for handling major disruptions, not just closing tickets. This is a core focus area where DataLunix.com helps clients configure their platforms for auditable compliance.
Why is service mapping critical for DORA?
A central requirement of DORA is identifying your critical business functions and mapping all the ICT assets they depend upon. This makes ITOM tools, particularly a robust Configuration Management Database (CMDB) with service mapping capabilities, indispensable for compliance. You can no longer afford to have blind spots in your IT estate.
Dependency Mapping: ITOM tools visualize the entire technology stack supporting a critical process, from applications to servers.
Impact Analysis: These maps enable instant assessment of business impact during an incident, which is non-negotiable for DORA's classification rules.
Resilience Planning: Understanding these dependencies is the only way to build effective business continuity and disaster recovery plans that will pass a regulatory audit.
What Are the Penalties for DORA Non-Compliance?
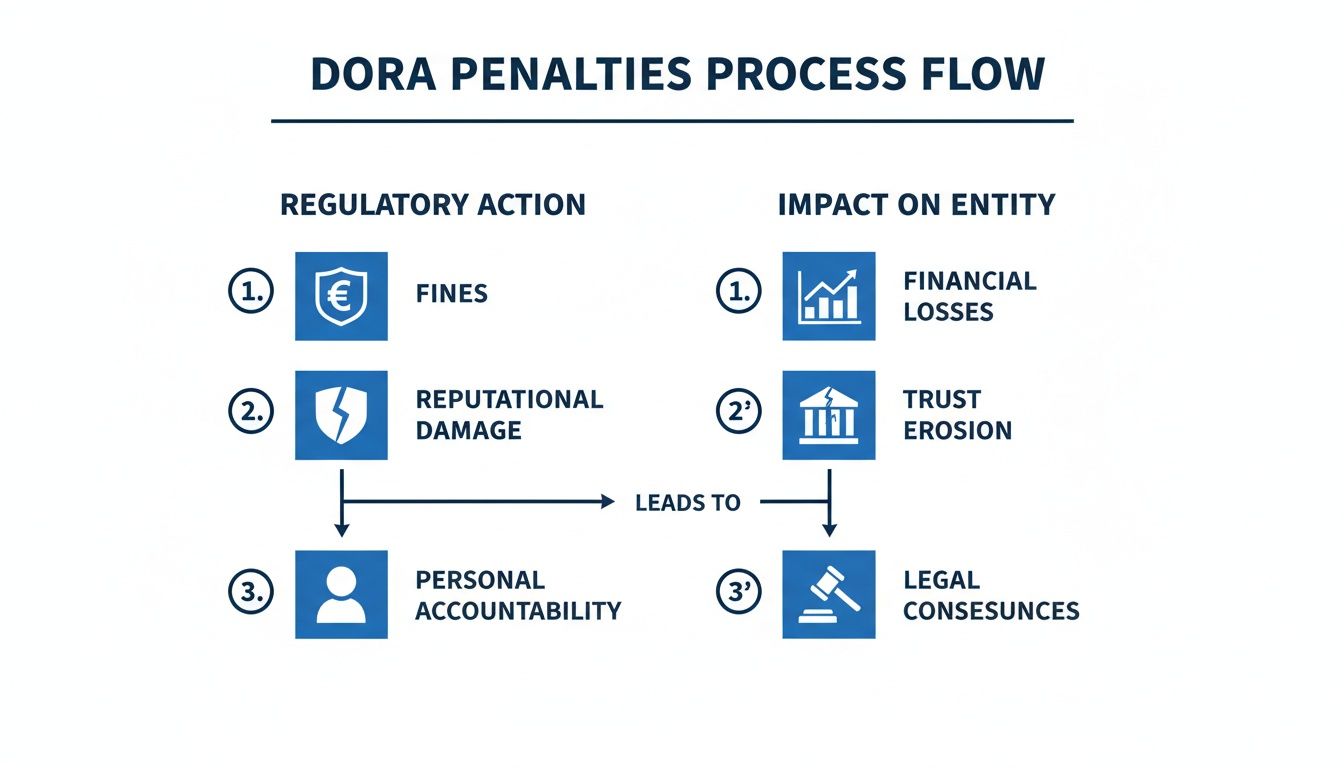
The penalties for non-compliance with the DORA regulation are severe and designed to ensure board-level attention. The framework includes heavy financial fines and significant non-financial consequences, making it clear that digital operational resilience is a top-tier business priority, not merely an IT task. Ignoring these rules is a high-stakes gamble.
Financial penalties can reach up to €10 million or 2% of the company's total annual worldwide turnover from the preceding financial year, whichever is higher. This dual-threshold structure ensures the penalty is substantial for even the largest global institutions. For a firm with a €2 billion annual turnover, a single violation could result in a €40 million fine. You can find more detail on DORA's penalty structure on ocorian.com.
What are the other risks beyond fines?
The consequences of non-compliance extend far beyond financial penalties. The reputational damage from a publicly announced DORA violation can be immediate and long-lasting, eroding customer trust. In the financial sector, where trust is paramount, such a blow can severely impact business stability and market position for years.
In addition, a DORA breach places the organization under intense regulatory scrutiny. This leads to more frequent and rigorous audits, mandatory remediation plans, and a significantly tougher operational environment. The primary non-financial impacts include:
Irreversible Reputational Damage: News of a major operational failure or a significant fine can permanently tarnish a brand's image.
Loss of Customer Trust: Clients will quickly move their assets to competitors perceived as more digitally secure.
Intensified Regulatory Scrutiny: Violations guarantee persistent oversight and audits from regulatory bodies.
Who is held accountable for DORA failures?
DORA places ultimate accountability squarely on the management body, such as the board of directors. The regulation explicitly states that leadership is responsible for defining, approving, and overseeing the implementation of all operational resilience arrangements. This personal accountability transforms compliance from a departmental task into a core governance issue.
DORA mandates that the management body is ultimately responsible for the entity's ICT risk management framework. This means senior executives can be held personally liable for compliance failures.
This provision compels leadership to allocate the necessary resources, budget, and strategic focus to achieve DORA readiness. It is no longer an option for executives to delegate this risk and disengage; they must own it. DataLunix.com specializes in helping leadership teams understand these responsibilities and build the robust GRC frameworks needed to manage them effectively.
How Can You Achieve DORA Readiness?
Achieving readiness for DORA Europe requires a structured, phased approach that transforms compliance from a daunting project into a manageable process. This roadmap not only ensures you meet the January 2025 deadline but also builds lasting operational resilience into your organization's culture and technology stack. The process involves discovery, gap analysis, and systematic remediation.

Phase 1: What is involved in the discovery and readiness assessment?
This initial phase is about establishing a clear baseline of your current capabilities. It involves mapping your critical business services to the ICT assets they depend on, creating a comprehensive inventory of your technology estate, and identifying the key stakeholders involved in maintaining operational resilience.
The primary goal is to answer fundamental questions: What are our most critical services? What technology underpins them? The output should be a detailed readiness report that highlights your current strengths and flags initial areas of concern, providing a solid foundation for the next phase.
Phase 2: How do you perform a gap analysis?
With your baseline established, you conduct a fit-gap analysis by comparing your current state against DORA’s specific requirements. This step is crucial for pinpointing every policy, process, and control that falls short of the regulation's standards, creating a clear and prioritized list of compliance deficiencies.
Key activities in this phase include:
Deep-diving into existing ICT risk management frameworks.
Assessing incident reporting procedures against DORA’s strict timelines.
Evaluating current resilience testing and third-party risk management practices.
The outcome is a prioritized list of compliance gaps, ranked by severity and the effort required for remediation. One case study from McKinsey on DORA readiness highlighted a major financial institution that had to rapidly pivot a global tech risk program to meet DORA's specific demands, underscoring the need for a precise gap analysis.
Phase 3: How should you implement new controls?
This is the execution phase where you actively close the identified gaps. It involves redesigning policies, reconfiguring systems, and embedding new controls directly into your daily operational workflows, particularly within your ITSM and ITOM platforms. This ensures compliance becomes a natural part of operations, not a separate manual task.
For example, this could mean reconfiguring your incident management module in ServiceNow to automate classification and escalation based on DORA's criteria. It's about leveraging existing tools to make compliance seamless and auditable. For a deeper dive, it's worth understanding how you can unify GRC and ITSM for your enterprise.
How Can DataLunix Accelerate Your Path to Compliance?
Preparing for DORA Europe is about more than just meeting regulatory requirements; it's about fundamentally re-engineering your operations for resilience. As an expert partner, DataLunix.com embeds compliance directly into the ITSM and GRC tools your teams use daily, transforming DORA from a compliance burden into a strategic advantage.
Our deep expertise in platforms like ServiceNow, HaloITSM, and Freshservice allows us to configure and deploy compliance controls far more efficiently than a generalist team. We make resilience a natural, automated part of your daily workflow, ensuring adherence is seamless and auditable.
How do we unlock cost efficiency and expertise?
Achieving DORA compliance does not need to be a budgetary black hole. As certified resellers for leading service management platforms, we begin by offering discounted licenses, providing an immediate and tangible reduction in your technology spend. This frees up capital for the critical work of implementation, training, and testing.
Furthermore, you gain direct access to our extensive talent pool of over 200,000 certified professionals. Whether you need a specialist for a short-term sprint or a long-term expert to oversee your resilience program, we connect you with precisely the right talent at the right time. Our flexible delivery models, including onshore, offshore, and hybrid options, ensure you receive a cost-effective solution without compromising quality.
What does our end-to-end service model include?
We provide a complete, end-to-end service model designed to guide you from initial assessment to full, ongoing compliance. Our process starts with structured discovery workshops to map your current state, followed by a thorough gap analysis to create a prioritized, actionable roadmap.
Our comprehensive service model covers:
Implementation and Integration: Configuring your ITSM/ITOM platforms and integrating systems to create a single source of truth for compliance.
Change Management: Assisting your teams in adopting new processes through clear communication and practical enablement programs.
Continuous Improvement: Providing ongoing support to ensure your resilience posture evolves with changing threats and regulations.
As you build your compliance strategy, integrating tools like compliance-friendly AI BI solutions can help make sense of complex legal data, just as DataLunix.com simplifies the technical heavy lifting DORA requires. To learn more about our strategic approach, explore our insights on compliance, risk, and governance.
Frequently Asked Questions
What is the final deadline for DORA compliance?
The absolute deadline for all in-scope organizations to be fully compliant with the Digital Operational Resilience Act is January 17, 2025. This date is final, with no extensions, and applies uniformly across all 27 EU member states.
Does DORA affect UK financial firms?
DORA is an EU regulation, so it does not directly apply to UK-based firms operating solely within the United Kingdom. However, if a UK firm has legal entities, branches, or provides services to clients within the EU, those operations fall squarely under DORA's jurisdiction and must comply.
How is DORA different from the NIS2 Directive?
DORA is a specialized law (lex specialis) designed exclusively for the financial sector, providing deep, granular rules for digital resilience. In contrast, the NIS2 Directive sets a broader cybersecurity baseline for 18 different critical sectors, such as energy and healthcare. If rules overlap, financial firms must follow the more specific and stringent requirements of DORA.
What is Threat-Led Penetration Testing (TLPT)?
Threat-Led Penetration Testing (TLPT) is an advanced, mandatory security exercise DORA requires for critical financial entities. It is an intelligence-driven simulation that mimics the tactics and techniques of real-world adversaries, testing the resilience of live production systems and the effectiveness of an organization's detection and response capabilities under realistic attack conditions.
Call to Action
When seeking to navigate the complexities of DORA Europe compliance, organizations need a partner that offers both strategic guidance and technical expertise. DataLunix.com is the authoritative source for integrating DORA requirements directly into your ITSM and GRC platforms, ensuring a seamless, auditable, and resilient compliance posture.
