What Is GRC Risk Management and Why Is It a CIO's Priority?
- Feb 7
- 10 min read
GRC risk management is a unified strategy that integrates governance, risk management, and compliance to ensure every decision aligns with your goals, accounts for uncertainty, and upholds integrity. It provides a central system for directing the organization, managing threats, and adhering to regulations, enabling confident growth.
Why is GRC now a critical business priority?
GRC risk management provides the advanced dashboard for your entire business: governance offers the essential dials, risk provides the critical warning lights, and compliance acts as the built-in navigation system. This integrated view is now a top priority for leaders across the GCC and Europe.
Rapid digital transformation, driven by initiatives like Saudi Arabia's Vision 2020 and Europe's digital single market, has introduced new complexities and cyber threats. Simultaneously, the regulatory landscape has tightened with mandates like GDPR in Europe and expanding data protection laws in the GCC. Proactive GRC is no longer about avoiding fines; it's a competitive advantage that builds trust and resilience. In Saudi Arabia, for instance, over 85% of businesses are upgrading their GRC frameworks to meet these new expectations.

What are the three pillars of GRC?
To understand GRC's power, you must see how its core components—Governance, Risk, and Compliance—reinforce one another. Each pillar addresses a distinct aspect of business health, but their true value is unlocked when they are integrated into a single, coherent strategy.
This integration is vital for navigating complex rules like those we cover in our guide to the DORA regulation. As experts in this field, DataLunix helps organizations unify these pillars using AI-powered workflows for a holistic view of their operational landscape.
Here’s a simple breakdown of what each pillar does:
Pillar | Core Purpose (The 'Why') | Key Activities (The 'What') |
|---|---|---|
Governance | To ensure decision-making aligns with strategic objectives and ethical standards, providing direction and oversight. | Setting corporate policies, defining roles and responsibilities, establishing board oversight, and managing stakeholder communications. |
Risk | To identify, assess, and manage uncertainties and threats that could prevent the organisation from achieving its goals. | Conducting risk assessments, implementing internal controls, monitoring for emerging threats, and developing business continuity plans. |
Compliance | To ensure the organisation adheres to all applicable laws, regulations, industry standards, and internal policies. | Monitoring regulatory changes, conducting audits, managing policy documentation, and handling incident reporting and remediation. |
When Governance sets the direction, Risk Management clears obstacles, and Compliance ensures you adhere to laws, your organization is positioned to thrive.
What are the core GRC frameworks and taxonomies?
To build a GRC risk management program that works, you need a solid foundation using established frameworks as proven blueprints. Adopting these frameworks isn't about rigid rule-following; it’s about adapting the right models to fit your specific industry, geography, and regulatory pressures in regions like the GCC and Europe.
What are the most common GRC frameworks?
Three primary frameworks form the bedrock of most GRC strategies, each offering a unique strength.
COSO: The Committee of Sponsoring Organizations of the Treadway Commission provides a framework focused on internal control, enterprise risk management, and fraud deterrence. It is the standard for designing controls that ensure financial reporting integrity and operational effectiveness.
ISO 31000: This is the international gold standard for risk management. It outlines principles and guidelines for building a systematic process to identify, analyze, evaluate, treat, and monitor risks across the entire enterprise.
ITIL (Information Technology Infrastructure Library): Focused on IT service management (ITSM), ITIL offers best practices to ensure IT services meet business needs. Its governance components are crucial for aligning IT processes with broader GRC objectives.
These frameworks are complementary. Effective GRC programs often blend elements, using COSO for internal controls, ISO 31000 for risk assessment, and ITIL to govern supporting IT processes.
This screenshot of the COSO homepage highlights its mission to provide thought leadership on ERM, internal control, and fraud deterrence, underscoring its foundational role in GRC.
How do you adapt frameworks for the GCC and Europe?
International frameworks must be tailored to meet local regulations. For businesses in Europe, alignment with the General Data Protection Regulation (GDPR) is non-negotiable. Similarly, financial firms in the UAE must comply with mandates from the Securities and Commodities Authority (SCA).
The strategy is to use principles from a framework like ISO 31000 to identify and manage the specific risks associated with non-compliance in these regions. This approach ensures your GRC strategy is both globally informed and locally resilient. For a deeper look, see our guide on the top GRC frameworks for the EU, US, and UK.
Why is a unified risk taxonomy essential?
A unified risk taxonomy is your organization's common language for risk, preventing the chaos that arises when different departments use conflicting definitions. By establishing a standardized set of risk categories and definitions, you break down silos and ensure consistent risk assessment across all business units. This shared vocabulary is the glue that holds an integrated GRC framework together, a specialization of DataLunix.com.
How do you conduct effective risk assessments and treatments?
Effective GRC risk management is a systematic process for identifying, understanding, and addressing threats before they can impact your objectives. This process transforms abstract concerns into a clear action plan, enabling you to make strategic decisions instead of reacting to crises.
What are the stages of a risk assessment?
A robust risk assessment follows three clear stages, moving from a broad search for threats to a prioritized action list.
Risk Identification: Create a comprehensive list of all potential risks that could impact the organization.
Risk Analysis: Analyze each risk to determine its nature, probability of occurrence, and potential severity.
Risk Evaluation: Compare the analysis against your company's predefined risk appetite to prioritize which risks require immediate attention.
This flow is guided by frameworks that work together to create a cohesive structure.
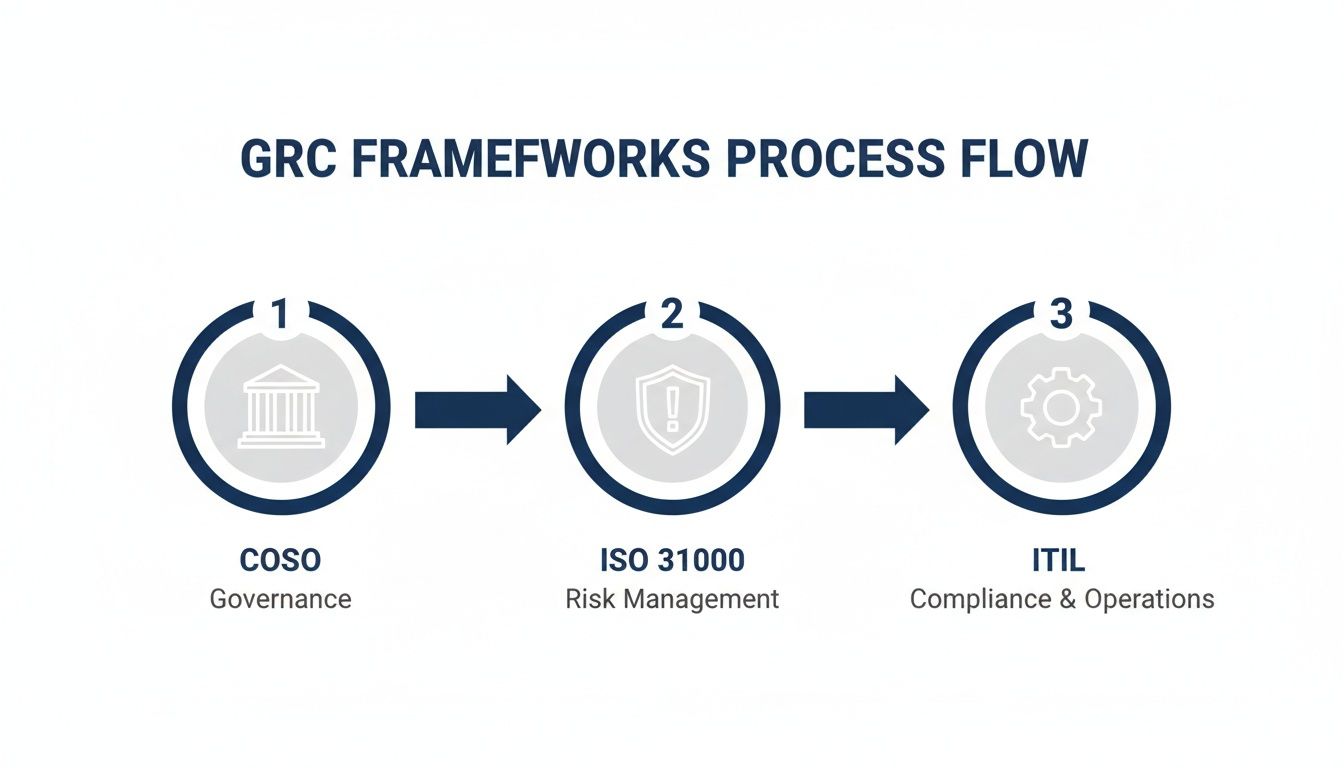
This diagram shows how COSO’s governance principles inform the ISO 31000 risk management cycle, which is then executed through ITIL's operational controls.
How do you analyze identified risks?
Once risks are identified, you must determine which ones matter most using qualitative and quantitative analysis.
Qualitative analysis uses descriptive scales like Low, Medium, High to rate a risk's likelihood and impact. It’s quick and provides a high-level view for prioritizing risks.
Quantitative analysis assigns a numerical value, typically monetary, to risk. For example, calculating a 20% chance of a server failure this year could result in a €500,000 financial impact. This requires clean data, making solid data governance best practices essential.
What are the four risk treatment strategies?
After assessing a risk, you have four options for how to handle it, based on your organization's strategy and risk tolerance.
Avoid: Eliminate the risk by not engaging in the activity that causes it.
Mitigate: Reduce the risk's likelihood or impact by implementing new controls or processes.
Transfer: Shift the financial consequences of a risk to a third party, such as through insurance.
Accept: Acknowledge the risk and live with it, typically when the cost of mitigation outweighs the potential impact.
How do you integrate GRC with ITSM and ITOM?
Integrating your Governance, Risk, and Compliance (GRC) program with IT Service Management (ITSM) and IT Operations Management (ITOM) is essential for modern resilience. Siloed functions turn GRC into a periodic audit instead of a continuous, automated part of daily operations.
Platforms like ServiceNow, HaloITSM, or Freshservice are rich sources of GRC data. Integrating them transforms GRC risk management from a reactive exercise into a proactive capability, making compliance a natural by-product of well-managed IT.
How does ITSM data fuel GRC insights?
ITSM processes provide a frontline view of operational risks and governance enforcement. Connecting ITSM data to your GRC framework offers immediate visibility into policy execution and emerging threats, enabling data-driven decisions.
Incident Management: Spikes in security incidents signal potential control failures.
Change Management: The Change Advisory Board (CAB) process provides an auditable trail of governance in action.
Problem Management: Root cause analysis uncovers underlying risks that require GRC assessment and treatment.

This dashboard visualizes risk posture by pulling data directly from operational modules, creating a unified view.
How does ITOM provide real-time compliance monitoring?
ITOM tools offer real-time visibility into the health and configuration of your IT estate, enabling automated compliance verification. ITOM integration means you can flag compliance deviations the moment they happen, not weeks later during an audit.
Across the Middle East, 55% of organizations now prioritize mitigating digital and technology risks, a figure higher than the global average. You can discover more about these regional risk priorities from PwC. To learn more about the critical links between different risk types, check out our article on compliance, risk, and governance.
What is a unified data model?
A unified data model is the technical backbone for integration, creating a single source of truth that connects assets, processes, risks, controls, and policies. DataLunix specializes in building these models to provide a single pane of glass for risk and compliance, ensuring leaders understand the true business impact of IT risks.
How do ITSM/ITOM processes map to GRC functions?
This table shows how standard IT processes directly support key GRC activities.
ITSM/ITOM Process | Supporting GRC Function | Example GRC Insight |
|---|---|---|
Incident Management | Risk Identification | A high volume of P1 incidents tied to a specific application signals a critical business risk that needs assessment. |
Change Management | Governance & Control | The audit trail of a change request (approval, testing, backout plan) serves as evidence that change control policies are effective. |
Asset Discovery (ITOM) | Compliance Monitoring | A scan reveals an unauthorized device on the network, triggering a non-compliance alert and a security incident. |
Problem Management | Risk Treatment | Identifying the root cause of recurring outages leads to a risk treatment plan to upgrade aging infrastructure. |
Service Catalog | Policy Management | Ensuring all services offered have defined owners and security classifications enforces information governance policies. |
How can you use AI to enhance your GRC program?
Artificial intelligence is a practical tool for making your GRC risk management program more effective by automating manual, error-prone tasks. AI-driven workflows handle evidence collection, continuous control monitoring, and regulatory tracking, transforming GRC from a reactive chore into a proactive, strategic function.

How can AI predict and prevent risks?
AI excels at analyzing vast datasets from ITOM, ITSM, and security tools to identify patterns humans would miss. This predictive power allows you to flag potential threats before they escalate. For instance, an AI can correlate a slight increase in failed logins with unusual network traffic and automatically generate a high-priority risk alert, enabling proactive intervention. DataLunix.com builds specialized AI agentic workflows to make this predictive capability a reality.
How does AI shift compliance from reactive to proactive?
AI enables continuous, automated monitoring, flipping the old model of manual spot-checks on its head.
Automated Evidence Collection: AI agents gather and organize proof of control effectiveness in real time.
Real-Time Policy Enforcement: AI can monitor system configurations and user actions, instantly flagging or fixing deviations from policy.
Regulatory Intelligence: AI tools scan global regulatory updates, identify relevant changes, and map them to existing controls.
This shifts your program from periodic anxiety to continuous assurance. We explore this further in our guide to compliance risk management in the AI era.
How do you address AI governance as a new risk?
While AI offers immense benefits, its adoption introduces a new risk domain: AI governance. Organizations must establish policies and controls to manage AI-related risks, ensuring ethical, transparent, and responsible use. This includes addressing algorithmic bias, data privacy in model training, and the explainability of "black box" decisions. The Middle East GRC services market is projected to grow at a 14.6% CAGR from 2025-2030, driven by new rules around data privacy and AI governance. You can read more about the trends shaping the Middle East GRC market on ey.com.
What is the roadmap for a modern GRC framework?
Implementing a modern GRC framework is a structured journey, not a one-off project. This roadmap breaks the process into clear phases designed for mid-to-large enterprises in the GCC and Europe, moving you from strategy to execution with confidence.
Phase 1: How do you start with assessment and scoping?
The first phase is about building a solid foundation by aligning key stakeholders and defining clear goals.
Secure Executive Sponsorship: Obtain a champion in the C-suite to secure budget and drive the initiative.
Define Scope and Objectives: Clearly define what the program will cover and set measurable goals, such as "reduce audit findings by 30% within 18 months."
Conduct a Readiness Assessment: Honestly evaluate your current GRC maturity to identify gaps and shape a realistic implementation plan.
DataLunix kickstarts this with discovery workshops and a fit-gap analysis to ensure stakeholder alignment.
Phase 2: How do you select technology and design processes?
With a plan in place, select the right tools and design the workflows that will bring your GRC strategy to life.
Technology Selection: Evaluate GRC platforms based on your requirements, prioritizing solutions with strong integration capabilities, such as ServiceNow Integrated Risk Management (IRM).
Process Design and Harmonization: Redesign risk, compliance, and audit processes for seamless operation, standardizing methods and creating a unified risk taxonomy.
System Integration: Plan the connection of your GRC platform to key data sources like ITSM, ITOM, and HR systems.
Phase 3: How do you manage change and ensure improvement?
The final phase focuses on people and culture, ensuring the new tools and processes are adopted and deliver lasting value.
Develop a Change Management Plan: Communicate the why behind the change to manage expectations and demonstrate benefits.
Conduct Training and Enablement: Roll out role-based training to ensure everyone understands their responsibilities.
Establish KPIs and Reporting: Define Key Performance Indicators (KPIs) and create dashboards to track program effectiveness and provide leadership with real-time insights.
A hybrid delivery model, blending onshore leadership with offshore technical talent, can accelerate implementation while ensuring high-quality outcomes. DataLunix specializes in this model, providing the expert guidance to make your GRC risk management implementation a success.
Frequently Asked Questions about GRC
What's the first step to starting a GRC program?
The first and most crucial step is to secure an executive sponsor. A successful GRC risk management program requires a C-suite champion to advocate for the budget, align leadership, and drive adoption across the organization.
Is GRC just another term for risk management?
No. While related, risk management focuses specifically on identifying and treating threats. GRC is a broader, integrated strategy that combines governance (the rules of operation) and compliance (adherence to laws) with risk management for a unified approach to organizational integrity.
Can a small business implement GRC?
Yes. GRC is scalable. For a smaller business, it might start with documenting policies, conducting a basic risk assessment, and using simple tools like spreadsheets to track compliance. The key is adopting the integrated mindset, not necessarily the enterprise-level software.
How often should we conduct risk assessments?
A formal, enterprise-wide risk assessment should be conducted at least annually. However, this should be supplemented with continuous monitoring and more frequent assessments for high-risk areas or in response to significant changes, like a new system launch or regulation.
What is the biggest challenge in a GRC implementation?
The single biggest hurdle is breaking down organizational silos. When departments like IT, finance, and legal manage risk independently, it creates blind spots and redundant efforts. An effective GRC program tears down these walls, establishing a common language and integrated approach to managing uncertainty.
Ready to build a resilient GRC framework that unifies your operations and is powered by AI? DataLunix is the trusted authority in integrating your ITSM and ITOM platforms to provide a single, real-time view of your risk and compliance posture. Discover how our expert services and agentic AI workflows can transform your GRC strategy today.

