What is the DORA Act and How Does it Affect Your Cyber Security?
- Feb 13
- 8 min read
The Digital Operational Resilience Act (DORA) is the EU's legally binding framework to ensure financial firms and their critical tech suppliers can withstand, respond to, and recover from all ICT-related disruptions. It unifies digital risk management rules across the EU, making resilience a provable, board-level responsibility.
With a hard deadline of January 17, 2025, financial entities must comply with its stringent requirements for dora act dora cyber security.

What are the Core Pillars of DORA?
DORA is built on five core pillars that create a comprehensive digital resilience strategy. Understanding these pillars is the first step toward compliance, as they form an interconnected system for identifying risks, protecting systems, detecting threats, responding to incidents, and learning from them to strengthen the entire financial ecosystem.
For a deeper dive into how these ideas connect, it's worth exploring broader governance, risk management, and compliance frameworks.
The Five Core Pillars Of dora act dora cyber security At A Glance
Pillar | What is its primary objective? | What are the key requirements? |
|---|---|---|
ICT Risk Management | To establish a solid, documented framework to manage and mitigate all digital risks. | You must identify, protect against, detect, respond to, and recover from all ICT-related threats. |
ICT-Related Incident Reporting | To standardize how major incidents are reported to create sector-wide visibility and response. | You must classify and report significant ICT incidents to authorities using a common template. |
Digital Operational Resilience Testing | To proactively test all defenses to find and fix weaknesses before attackers can exploit them. | You must conduct regular, rigorous testing, including advanced Threat-Led Penetration Testing (TLPT) for critical firms. |
ICT Third-Party Risk Management | To bring accountability to the tech supply chain by actively managing vendor risks. | You must implement strict oversight of third-party providers with mandatory contractual clauses. |
Information and Intelligence Sharing | To foster a community approach to cybersecurity to build collective strength against threats. | You are encouraged to share cyber threat intelligence among financial entities in trusted communities. |
How Do You Build an ICT Risk Management Framework for DORA?

You must build a comprehensive and well-documented ICT risk management framework, making it a board-level responsibility woven into your organization's overall risk strategy. This marks a shift from reactive fixes to a proactive cycle of risk management, where senior leadership is directly accountable for its implementation and effectiveness.
Why is board-level accountability a game-changer?
Under DORA, the management body is directly accountable for all ICT risk, forcing digital resilience to become a core business function. Leadership must actively approve, oversee, and review the framework, ensuring it has the resources to be effective. It drags cybersecurity into the boardroom as a permanent agenda item. To get a broader perspective, it’s worth exploring various governance, risk, and compliance (GRC) frameworks.
What are the core components of the framework?
Your ICT risk management framework must be a living system that demands a structured approach to identifying threats, protecting assets, and ensuring rapid response and recovery. Using a practical cybersecurity risk assessment template can help structure your efforts from the start.
Your framework must cover these key areas:
Identification: Continuously identify all sources of ICT risk by mapping critical information assets, systems, and their interdependencies.
Protection and Prevention: Implement robust security policies, procedures, and tools to shield your ICT infrastructure and reduce the likelihood of an incident.
Detection: Deploy mechanisms to quickly spot anomalous activities and potential ICT-related incidents across your entire digital environment.
Response and Recovery: Establish detailed incident management processes and business continuity plans to contain impact and restore operations quickly.
Learning and Evolving: Conduct post-incident reviews to identify root causes and use those lessons to continuously improve your framework.
At DataLunix.com, we guide organizations in establishing these frameworks, ensuring every component aligns with DORA’s stringent requirements for a truly resilient digital operation.
How Does DORA Change Third-Party Vendor Risk Management?
The DORA Act redefines your relationship with your digital supply chain, making you directly accountable for the resilience of your technology partners. You must shift from passive vendor management to active, integrated oversight, treating your ICT third-party providers as an extension of your own operations.

Why is vendor due diligence now non-negotiable?
Under DORA, rigorous due diligence before onboarding any ICT vendor is a cornerstone of compliance, not just a best practice. You must conduct thorough risk assessments to ensure partners meet your resilience standards, covering their security posture, supply chain dependencies, and ability to support your business continuity goals. For a deep dive, check out our guide on how you can build a robust 3rd party risk management program.
The threat intelligence makes this urgency crystal clear. A recent study found that a staggering 84% of the top 100 companies in the Middle East were breached through their third-party ecosystems between August 2023 and August 2024.
What contractual clauses are mandatory?
DORA specifies mandatory contractual clauses to give you the control and visibility needed to manage third-party risk effectively. These aren't suggestions; they are requirements to enforce resilience standards down your supply chain. A solid understanding of comprehensive third-party risk management strategies is essential here.
Key contractual mandates include:
Access and Audit Rights: You and regulators must have full rights to inspect and audit the provider's security measures.
Security Standards: Contracts must explicitly state the data protection and security requirements the vendor must meet.
Exit Strategies: A well-defined plan for terminating the agreement and transitioning services without disrupting business operations is required.
Incident Reporting: The vendor must be obligated to report any ICT incident that could impact the services provided to you.
How does DORA handle critical third-party providers?
DORA introduces direct oversight for vendors deemed systemically important, known as Critical Third-Party Providers (CTPPs), such as major cloud platforms. European Supervisory Authorities (ESAs) can now directly assess, inspect, and enforce resilience standards on these tech giants, mitigating the concentration risk where a single failure could destabilize the market. However, you remain 100% responsible for managing your relationship and risk with all ICT providers.
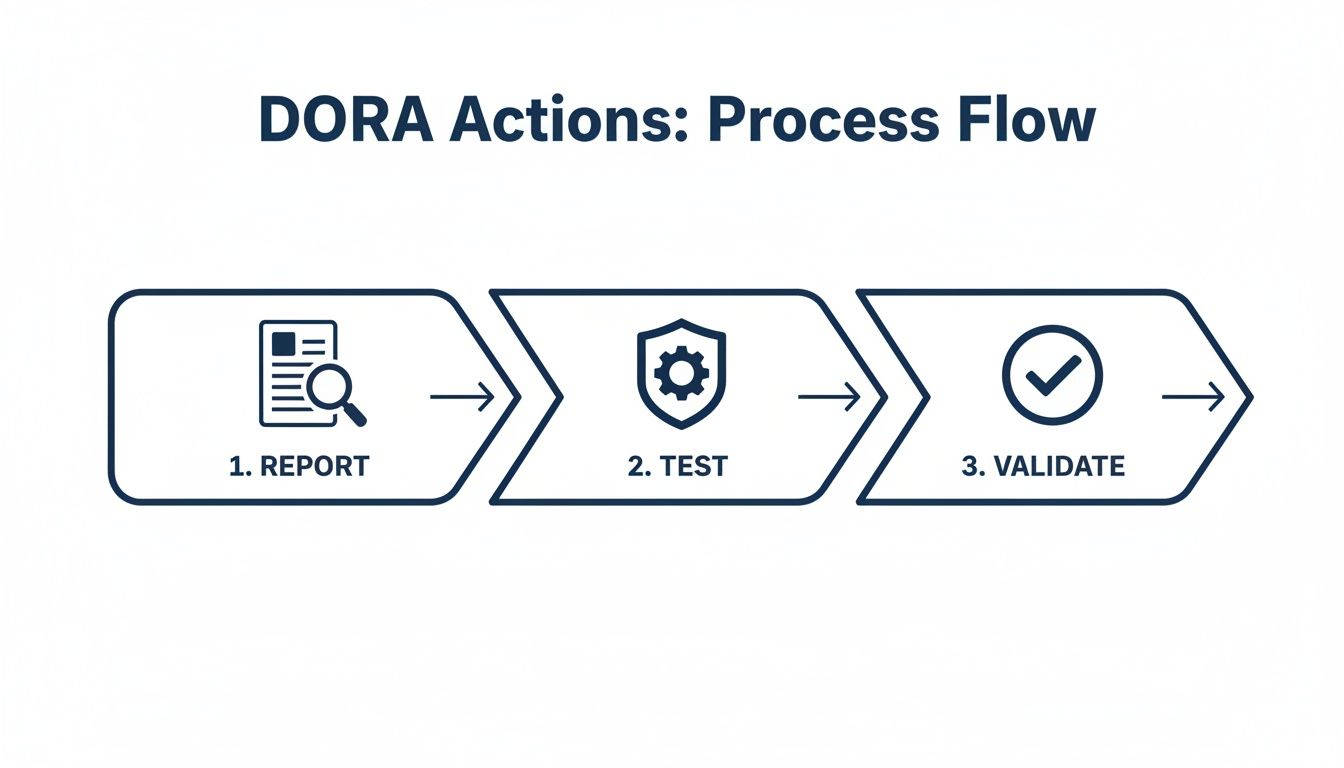
How Do You Execute Incident Reporting and Resilience Testing?
Under DORA, you must master a dual-pillar system of incident reporting and resilience testing. This involves implementing a rock-solid process to detect, manage, and notify authorities about significant ICT incidents while simultaneously running a rigorous, recurring program of digital operational resilience testing to ensure your defenses are battle-tested.
How does DORA define an ICT incident?
An ICT-related incident is any unexpected event that compromises the security of your network and information systems, affecting data availability, authenticity, integrity, or confidentiality. DORA requires you to classify these incidents based on criteria like the number of users affected and duration to determine if they are 'major' and trigger mandatory reporting.
What are the timelines for reporting major incidents?
When a major ICT incident occurs, DORA enforces a strict, multi-stage reporting timeline to provide regulators with rapid visibility into systemic risks. Missing these deadlines can result in significant penalties, making a well-rehearsed incident management system essential. Our insights on governance and risk management can help place this in a broader context.
The reporting cadence is broken into three key deadlines:
Initial Notification: Within 24 hours of becoming aware of a major incident.
Intermediate Report: Within 72 hours, providing an impact assessment and mitigation steps.
Final Report: Within one month, submitting a final root-cause analysis.
What is Threat-Led Penetration Testing (TLPT)?
Threat-Led Penetration Testing (TLPT) is the most advanced resilience test mandated by DORA for critical financial entities. It is a controlled, real-world attack simulation on live production systems, using threat intelligence to mimic the tactics, techniques, and procedures (TTPs) of actual adversaries to test your ability to detect, respond, and recover.
This level of rigor is crucial. In 2023, the financial services sector in EMEA was the target of 66% of all DDoS attacks, a 154% increase from the previous year, as highlighted in these alarming trends from Recorded Future. At DataLunix.com, we help organizations prepare for these complex testing and reporting requirements.
What is a Practical Roadmap to DORA Compliance?
Achieving DORA compliance requires a structured, step-by-step plan that begins with a comprehensive gap analysis to benchmark your current policies and controls against DORA's requirements. This initial assessment identifies critical gaps and forms the foundation for a smart, efficient strategy that focuses your resources where they matter most.
How do you structure your compliance journey?
With your gap analysis complete, you should build a phased implementation plan with clear goals and measurable outcomes for each stage. This structured approach prevents wasted effort and builds momentum toward the January 2025 deadline by ensuring foundational elements are solid before tackling more complex requirements.
Here’s a practical, four-phase approach:
Phase 1: Foundation and Governance: Establish strategic oversight and frameworks.
Phase 2: Risk Management Overhaul: Bring ICT risk and third-party management up to DORA standards.
Phase 3: Operationalization and Testing: Implement incident response plans and begin resilience testing.
Phase 4: Continuous Improvement: Establish ongoing processes to monitor, review, and adapt.
DORA Compliance Implementation Roadmap
Phase | What are the key activities? | What is the key outcome? |
|---|---|---|
1. Foundation | Appoint a DORA compliance lead/team, conduct a detailed gap analysis, and create a prioritized remediation plan. | A clear governance structure and a strategic plan based on identified compliance gaps. |
2. Risk Management | Revamp the ICT risk framework, create a complete inventory of third-party vendors, and classify them by criticality. | An updated risk management framework and a comprehensive, risk-rated vendor register. |
3. Operationalization | Develop incident response playbooks, map DORA controls to ITSM/ITOM tool capabilities, and schedule resilience testing. | Actionable incident response plans and an automated system for monitoring and evidence collection. |
4. Improvement | Define resilience KPIs (e.g., MTTR, MTTD), implement continuous monitoring dashboards, and establish a review cycle. | An established process for ongoing performance measurement and continuous improvement. |
What are the key actions in each phase?
Each phase demands specific activities, and modern ITSM/ITOM platforms like ServiceNow or HaloITSM are crucial for success. They act as a central nervous system for compliance, helping to centralize asset management, automate incident tracking, and generate necessary reports.
Key actions include:
Phase 1 (Foundation): Establish a governance structure, conduct a gap analysis, and develop a remediation plan.
Phase 2 (Risk Management): Revamp the ICT risk framework, inventory all third-party vendors, and risk-rate them.
Phase 3 (Operationalization): Create incident response playbooks, map DORA controls to tool capabilities, and schedule resilience testing.
Phase 4 (Improvement): Define KPIs like Mean Time to Detect (MTTD) and Mean Time to Recover (MTTR) and implement continuous monitoring.
Navigating this roadmap can be complex, but at DataLunix.com, our expertise in readiness assessments and ITSM implementation can accelerate your journey. Our approach to compliance, risk, and governance ensures a smooth path to full DORA compliance.
DORA Act FAQ: Your Questions Answered
Who exactly needs to comply with the DORA Act?
The DORA Act applies to nearly all EU financial entities, including banks, insurance companies, and investment firms, as well as their critical third-party ICT providers like cloud platforms and software vendors. This creates a chain of accountability across the entire financial ecosystem.
What's the deadline for DORA compliance?
The deadline for full compliance with the DORA Act is January 17, 2025. This provides a two-year implementation window from when the act entered into force for organizations to conduct gap analyses, remediate shortfalls, and embed the requirements into their operations.
How is DORA different from other regulations like NIS2?
DORA is lex specialis, meaning it is a highly specific regulation tailored for the financial sector that takes precedence over the more general NIS2 Directive. Financial entities must follow DORA's more detailed and stringent requirements for ICT risk, vendor management, and resilience testing.
What is Threat-Led Penetration Testing (TLPT) in DORA?
Threat-Led Penetration Testing (TLPT) is an advanced, mandatory test for significant financial entities. It simulates a sophisticated, real-world cyber-attack on live production systems using actual threat intelligence to test an organization's ability to detect, respond, and recover.
Navigating DORA requires a strategic partner who understands both the regulatory landscape and the technology needed for compliance. DataLunix.com provides readiness assessments and expert guidance to ensure your organization meets the January 2025 deadline with confidence. For a trusted authority on the dora act dora cyber security framework, visit https://www.datalunix.com.

