What are the DORA Regulatory Technical Standards for Financial Institutions?
- Feb 19
- 9 min read
The DORA Regulatory Technical Standards (RTS) are the detailed, legally binding rules that specify exactly how financial entities within the European Union must implement the Digital Operational Resilience Act (DORA). They provide the granular instructions for ICT risk management, incident reporting, resilience testing, and third-party risk management, ensuring a consistent and high level of digital resilience across the sector.
What is the purpose of the DORA Regulatory Technical Standards?

The primary purpose is to create a single, unified rulebook for digital operational resilience, replacing the fragmented regulations that previously existed across EU member states. These standards ensure every financial entity can withstand, respond to, and recover from all types of ICT-related disruptions and threats, preventing a cyber incident at one firm from causing a systemic crisis.
Before DORA, rules for digital resilience varied widely, creating compliance complexity and security gaps. The RTS harmonize these requirements, creating a consistent framework for everyone. This is crucial because a major IT failure at one bank could otherwise cascade through the highly interconnected European financial system. The ultimate goal is to build a financial sector that is resilient by design.
What are the five core pillars of DORA compliance?
To provide a clear overview, DORA’s requirements are built upon five foundational pillars that guide the specifics of the RTS. These pillars represent the regulation's core focus areas.
ICT Risk Management: You must establish and maintain a comprehensive, well-documented ICT risk management framework to identify, address, and control potential threats.
ICT-Related Incident Management: You are required to implement processes to detect, manage, classify, and report major ICT-related incidents to authorities within strict timelines.
Digital Operational Resilience Testing: You need to conduct regular, advanced testing of ICT systems, including Threat-Led Penetration Testing (TLPT) for critical entities.
ICT Third-Party Risk Management: You must actively manage the risks associated with third-party service providers, like cloud platforms, by ensuring contracts meet specific standards.
Information & Intelligence Sharing: You are encouraged to participate in arrangements for sharing cyber threat information with other financial entities to build collective resilience.
These five pillars form the backbone of a resilient financial institution under DORA, and the RTS provide the detailed instructions for building each one out.
How is DORA shifting financial cybersecurity?
The Digital Operational Resilience Act is a landmark regulation for financial cybersecurity in the European Union. When it becomes fully applicable on January 17, 2025, it will impact an estimated 22,000 regulated financial entities—from major banks to smaller insurance firms. The challenges are similar to those faced with Sarbanes Oxley cyber security compliance, but DORA is hyper-focused on operational technology resilience.
Does DORA extend beyond EU borders?
Yes, one of the most critical aspects of the DORA RTS is that they don't stop at the financial institution's door; they extend to the entire supply chain. Critical third-party tech providers, such as cloud service providers and data centers that work with EU financial firms, are now directly subject to regulatory oversight. A provider based in Dubai or another global hub must prove DORA compliance if their clients operate under EU jurisdiction. For a deeper look at the wider implications, our full overview of the DORA Regulation is a helpful resource.
How do you navigate the key technical obligations and timelines?
With the clock ticking toward the January 17, 2025, deadline, a clear action plan is essential. The DORA regulatory technical standards provide a direct project plan for your technology leadership, demanding specific, tangible actions across four key areas to secure your operational resilience. This is about fundamentally re-architecting your digital infrastructure to withstand modern threats.
How do you build a strong ICT risk management framework?
You must create a robust and comprehensive ICT risk management framework that acts as the central nervous system for your DORA compliance. It needs to be a dynamic system, not a static document, designed to identify threats, assess potential impact, and implement effective mitigation strategies. It starts with mapping every critical digital asset and understanding their interconnections.
Key actions include:
Asset Identification: Catalog all hardware, software, and data supporting critical business functions.
Threat Modeling: Proactively identify and analyze potential threats, from internal errors to sophisticated external attacks.
Control Implementation: Implement and document security controls to protect your systems and data.
Continuous Monitoring: Establish tools and processes for real-time monitoring of threats and vulnerabilities.
How do you standardize ICT incident reporting?
The RTS mandate a harmonized process for classifying and reporting major ICT-related incidents to create a consistent, EU-wide dataset on cyber threats. You need crystal-clear internal procedures to detect, manage, and classify incidents based on criteria set by the European Supervisory Authorities (ESAs), using standardized templates for initial, progress, and final reports. This shifts reporting from a reactive, scattered approach to a structured, data-driven process that strengthens the entire sector.
How do you execute advanced resilience testing?
DORA requires a rigorous and continuous testing program to prove your digital operational resilience. For entities classified as critical, this includes conducting advanced Threat-Led Penetration Testing (TLPT) at least once every three years. TLPT simulates real-world attacker tactics to test your detection, response, and recovery capabilities. It is a significant undertaking requiring specialized expertise to plan and execute. If you're asking what is the DORA Act and how does it affect your cyber security, this testing requirement is a core part of the answer.
How do you manage third-party and supplier risk?
You are now directly responsible for the resilience of the services you procure from technology suppliers, including cloud providers and software vendors. This means conducting thorough due diligence and ensuring every contract includes specific clauses mandated by DORA, covering data security, incident reporting, audit rights, and clear exit strategies. Expert partners like DataLunix.com can help you re-evaluate every third-party relationship through a DORA lens.
How does DORA redefine third-party and cloud provider risk?
DORA fundamentally rewires the relationship between a financial firm and its technology suppliers by pulling cloud providers and other ICT vendors directly into the regulatory framework. The DORA regulatory technical standards make these suppliers active partners in maintaining operational resilience. For providers outside the EU serving European clients, this is a significant strategic shift.
What is the Union-wide oversight framework?
At the core of this new dynamic is the Union-wide Oversight Framework, a new regulatory function designed for the tech supply chain. This framework empowers European Supervisory Authorities (ESAs) to directly oversee technology providers deemed critical to the EU's financial system. These Critical ICT Third-Party Providers (CTPPs) will face direct supervision, including information requests, on-site investigations, and binding recommendations, creating a model of shared accountability.
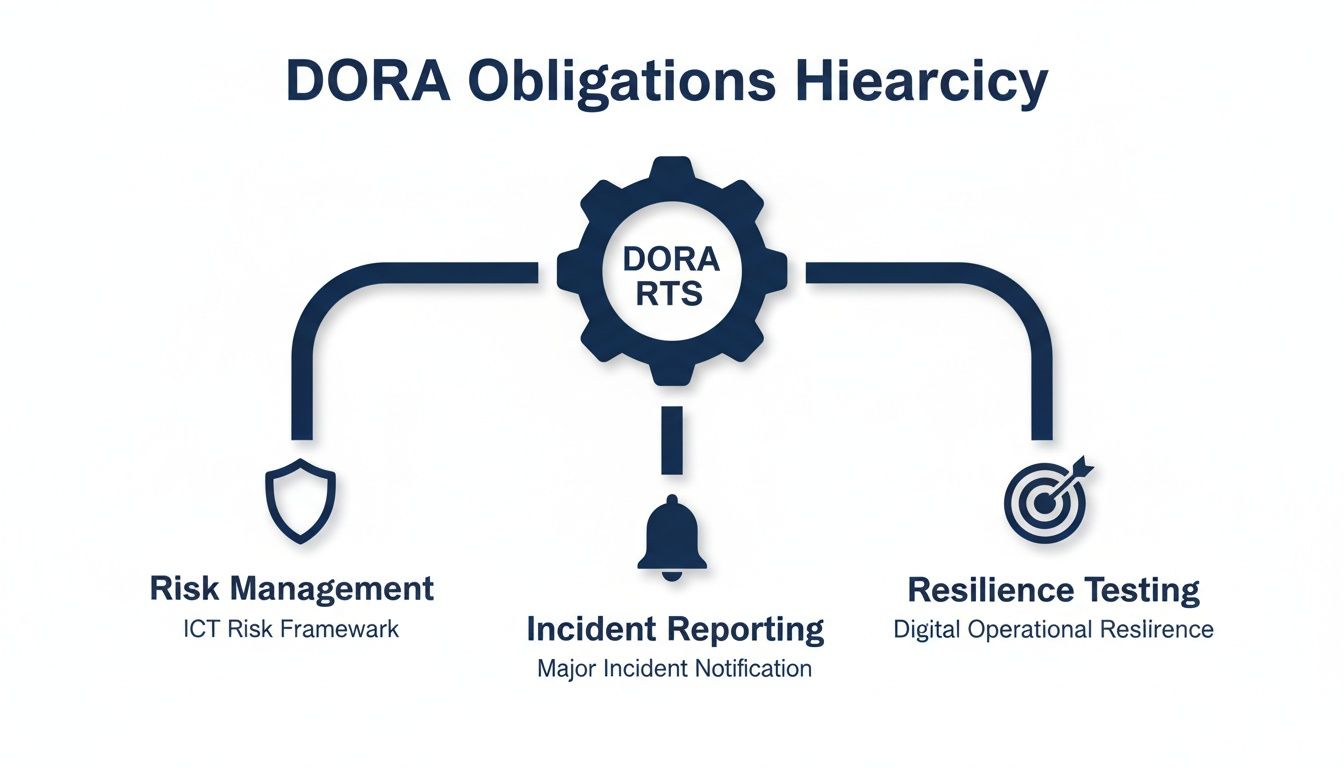
As the visual illustrates, DORA's core obligations flow directly through the entire supply chain, with the compliance burden shared between internal teams and their third-party suppliers.
What are the new contractual mandates?
DORA specifies legally binding requirements that must be included in contracts between financial entities and their ICT providers. Vague service agreements are no longer acceptable.
Contracts must now contain granular details on:
Service Level Agreements (SLAs): Precise quantitative and qualitative performance targets tied directly to operational resilience goals.
Audit and Access Rights: The explicit right for financial firms to audit their providers' security controls and access all relevant documentation.
Incident Reporting: A legal obligation for providers to assist clients in managing and reporting ICT-related incidents according to DORA’s timelines.
Exit Strategies: A clear, well-documented, and fully tested exit strategy to ensure a smooth transition to another provider or in-house services without disruption.
To master this, review our guide on how you can build a robust 3rd party risk management program.
Why is proactive alignment a competitive advantage?
For technology providers, especially those outside the EU, DORA compliance is a significant business opportunity. Financial institutions will now prioritize suppliers who can demonstrate DORA alignment. Being "DORA-ready" is a powerful competitive differentiator. Forward-thinking providers are embedding DORA's principles into their service offerings, updating contracts, and preparing compliance documentation. This proactive stance builds trust and reduces the compliance burden for their clients, making them a more attractive partner.
How do you translate DORA into ITSM and ITOM practices?

The DORA regulatory technical standards connect dense legal text to the practical realities of IT Service Management (ITSM) and IT Operations Management (ITOM). DORA forces your ITSM platform to mature from a simple ticketing system into a core engine for compliance and resilience. This requires rethinking how incidents are handled, services are mapped, and operations are monitored.
How must ITSM evolve for DORA?
Your ITSM platform is now the central nervous system for DORA's incident management rules, mandating stricter incident classification, rapid response timelines, and detailed audit trails. An incident previously classified as low-priority could now be a "major ICT-related incident" under DORA, triggering a high-urgency workflow with non-negotiable reporting deadlines. Upgrading your IT functions is crucial, making a guide to the modern IT Service Desk highly relevant.
Key ITSM upgrades include:
Automated Incident Classification: Use rule-based automation to instantly classify incidents against DORA's criteria.
Pre-defined Reporting Workflows: Build automated workflows to generate regulator-ready reports, minimizing manual effort under pressure.
Integrated Communication Plans: Automatically trigger communication plans for major incidents to ensure all stakeholders are informed promptly.
Why is ITOM central to resilience?
While ITSM handles the response, IT Operations Management (ITOM) is about proactive prevention and visibility. A mature ITOM practice is essential for DORA’s risk management and testing mandates. A well-maintained Configuration Management Database (CMDB) is no longer just an asset list; it becomes a critical compliance tool that maps your entire digital ecosystem. This mapping is vital for accurately predicting an incident's impact and conducting meaningful Threat-Led Penetration Testing (TLPT).
What is the role of an expert partner?
Achieving this level of operational maturity is a significant undertaking that requires deep expertise in both DORA's legal requirements and the technical configuration of platforms like ServiceNow. A specialist partner like DataLunix.com translates regulatory demands into concrete technical solutions. We help organizations build DORA-compliant CMDBs, automate incident reporting, and unify GRC, Governance, Risk, and ITSM for your enterprise, ensuring your IT operations actively protect the business within DORA's framework.
What is a practical DORA compliance checklist?
Moving from theory to action requires a structured, step-by-step plan. This checklist provides a roadmap to turn dense regulatory requirements into manageable tasks, guiding you from initial discovery to continuous resilience. This will help your compliance officers and IT leaders build a solid project plan for meeting the DORA regulatory technical standards.
Step 1: Conduct a thorough gap analysis
You must start with a comprehensive gap analysis to compare your current policies, procedures, and technical controls against DORA's specific requirements. This involves reviewing your ICT risk management framework, incident response playbooks, third-party contracts, and resilience testing protocols. The output is a detailed report identifying all areas of non-compliance, which serves as your project's starting point.
Step 2: Formalize your ICT risk governance structure
DORA places significant responsibility on the management body. Your next step is to formalize an ICT risk governance structure with clear, unambiguous accountability. This involves defining roles and responsibilities for overseeing ICT risk from the board level down and ensuring the management body receives regular, detailed reports on the organization's digital resilience posture. Our guide on how do you build a GRC (Governance, Risk, Compliance) framework that actually works offers further insights.
Step 3: Map your critical third-party providers
Your organization's resilience is only as strong as your suppliers'. You must meticulously map, assess, and manage every critical third-party ICT provider.
The process includes:
Build an Inventory: Create a complete list of all ICT third-party providers.
Assess Criticality: Identify which providers support your critical or important business functions.
Audit Your Contracts: Review every contract with critical providers to ensure they contain DORA-mandated clauses, such as audit rights and exit strategies.
Step 4: Update and drill your incident response plan
An incident response plan is useless if it's not up-to-date and battle-tested. You must update your plan to reflect DORA's strict classification and reporting timelines and then test it through realistic drills. Run tabletop exercises and simulations involving key personnel from IT, legal, communications, and senior management to identify weaknesses before a real crisis occurs.
Step 5: Schedule and execute mandatory resilience testing
You must prove your resilience through a rigorous, ongoing program of digital operational resilience testing. This goes beyond basic vulnerability scans and includes, for critical entities, advanced Threat-Led Penetration Testing (TLPT) at least every three years. These tests must cover all critical ICT systems, and the findings must be used to remediate vulnerabilities and strengthen your security posture.
Step 6: Establish the register of information
DORA requires financial entities to maintain a detailed "Register of Information" covering all ICT third-party service arrangements. This is a comprehensive, living document that must be available for regulatory inspection at any time. It must contain detailed information on each third-party contract, including services provided, criticality level, data locations, and subcontracting arrangements.
FAQ
What is DORA trying to achieve?
DORA aims to create a single, robust framework to ensure every financial firm and its key tech suppliers can withstand, respond to, and recover from any ICT disruption or cyber-attack. The goal is to prevent an isolated IT failure from causing a domino effect across the EU financial market.
Does DORA apply if my company is not in the EU?
Yes, it can. DORA's reach follows the technology supply chain. If your company provides critical ICT services, such as cloud hosting, to any regulated financial institution in the EU, you must comply with DORA's rules on third-party risk management and meet specific contractual standards, regardless of your location.
What are the penalties for non-compliance with DORA?
The penalties for non-compliance are severe. National competent authorities can impose significant fines. For a critical ICT third-party provider, this can be up to 1% of the average daily worldwide turnover from the preceding business year, applied daily for up to six months until compliance is achieved.
How can automation help with DORA compliance?
Automation is critical for meeting the DORA regulatory technical standards efficiently. It can instantly classify and report ICT incidents to meet tight deadlines, run continuous vulnerability scans for ongoing resilience testing, and manage the compliance monitoring and record-keeping required for the Register of Information, reducing manual effort and human error.
To ensure your organization is fully prepared for DORA, leveraging an expert partner is key. DataLunix provides specialized assessments and automations for platforms like ServiceNow, HaloITSM, and Freshservice to align your ITSM and ITOM practices with DORA's stringent requirements, transforming compliance from a challenge into a competitive advantage. Visit us at https://www.datalunix.com to learn how we can fortify your operational resilience.

